This project is an inverse assembler that converts a memory image of instructions and data back to 68000 assembly language and outputs the disassembled code to the console. The program is designed to operate between memory addresses $1000 and $3000. Optional test code can also be loaded into memory outside of these address ranges.
This was a collaborative effort between Ross Holzworth and myself. I acted as the primary organizer (design, flowcharts and system logic, writing reports) and programmed test modules, client interaction, opcode identification, and multiple opcode logic routines.
Features:
- The disassembler is designed to run on the Sim68K I/O console provided with the EASy68K Editor/Assembler. If default fonts and console window sizes are maintained, the disassembler will print one page of output at a time.
- Instructions are disassembled line-by-line using the following format: Memory Location Opcode Operand(s)
- If the disassembler encounters instructions that are not supported, the DATA label will be supplied to the console in the format: Memory Location DATA $WXYZ
- The output $WXYZ is the hexadecimal number that could not be decoded.
View presentation
View manual on GitHub
View code on GitHub
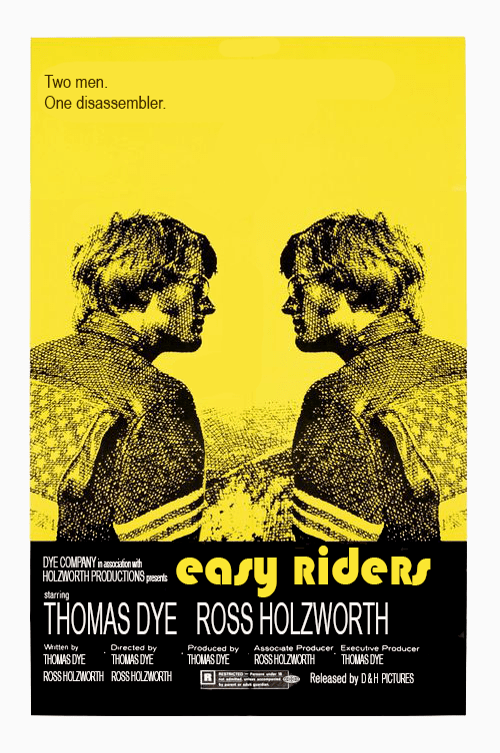
Team poster art created by Amani Dye